London – Operation Petya, a ransomware similar to Wannacry, attacked a large number of computers on a global scale which prompted several international experts demanding the National Security Agency (NSA) to exert more efforts to fight these viruses.
Wannacry is a global ransomware which attacked computers on May 13 and reportedly affected more than 300 thousand systems and servers around the world within 72 hours.
British security experts said that Petya attack occurred in different areas around the world and they believe it started in Ukraine.
The cyber-attack has caused disruption around the world and infected companies in 64 countries, including banks in Ukraine, Russian oil giant Rosneft, British advertising company WPP and US law firm DLA Piper.
Fingers are pointing towards MEDoc, Ukrainian tax-filing software, as the source of the infection, although the company denies it. Usually, malware generally infiltrates networks via email attachments that users click on in error.
Microsoft described the method as “a recent dangerous trend”, according to BBC.
A number of security experts, believe MEDoc to be the source of transfer of the malware.
British malware expert Marcus Hutchins, credited with ending the WannaCry ransomware outbreak, claim to have logs that reveal MEDoc as the source.
“It looks like the software’s automatic update system was compromised and used to download and run malware rather than updates for the software,” Hutchins told BBC.
It was not yet clear how it had been compromised, he added.
MEDoc has denied the claims, in a Facebook post, but in a blog post analysing how the infection had taken hold on Windows machines, Microsoft also points the finger at the accounting software.
“Active infections of the ransomware initially started from the legitimate MEDoc update process,” it writes.
Electronic Weapon
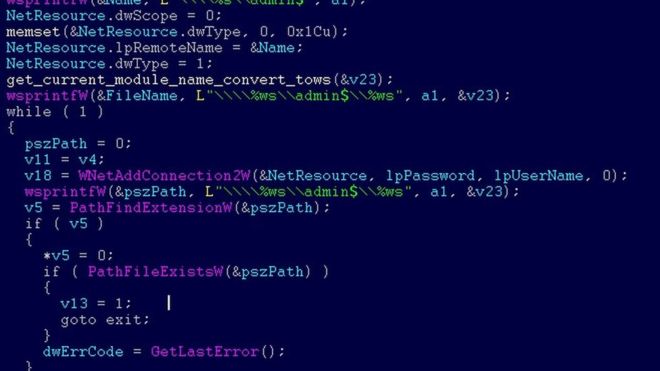
The ransomware was spread using a Windows vulnerability known as Eternal Blue, discovered by the National Security Agency and leaked online.
Global chief information officer at New-Jersey-based IDT Golan Ben-Oni said that NSA needs to take a leadership role in working closely with security and operating system platform vendors such as Apple and Microsoft to address the plague that they’ve unleashed.
New York times reported Ben-Oni warning federal officials that more serious attacks were probably on the horizon.
In March, Microsoft patched updates that deal with the vulnerability in Windows software used by Eternal Blue, but hundreds of thousands of groups around the world failed to properly install the fix.
The company announced that using the latest version of its software will protect users from both viruses, but experts stated that issuing an update doesn’t mean it will actually be used.
“Just because you roll out a patch doesn’t mean it’ll be put in place quickly,” said Carl Herberger, vice president for security at Radware.
“The more bureaucratic an organization is, the higher chance it won’t have updated its software,” he added.
Researchers at F-Secure, a Finnish cybersecurity firm, believe that the ransomware used at least two other ways to spread on Tuesday including stealing victims’ credentials, even those who used the Microsoft patch could be vulnerable and potential targets for later attacks.
White House Reassures
The White House National Security Council said in a statement that the US is investigating the attack but that there is currently no risk to public safety, Reuters reported, and the US government is “determined to hold those responsible accountable.”
NSA didn’t respond to claims that EternalBlue was leaked by Shadow Brokers, group of hackers linked to Russia. North Korea is accused of spreading WannaCry virus. Both governments denied the allegations.
So far, although the attack has spread around the globe, it does not appear to have generated a great deal of ransom payments. Like WannaCry, the attack locks users out of their systems and files and demands a payment of $300 in the cryptocurrency bitcoin.
The attack is more severe this time because users are not able to run their computers unless they pay the ransom.
Spread of Virus
Ukraine suffered more than 60 per cent of the attacks, followed by Russia with more than 30 per cent, according to initial findings by researchers at the cybersecurity firm Kaspersky Lab.
In Kiev, Ukrainian government said several of its ministries, local banks and metro systems had been affected. A number of other European companies, including Rosneft, the Russian energy giant; Saint-Gobain, the French construction materials company; and WPP, the British advertising agency, also said they had been targeted.
The cyber attack has hit the property arm of France’s biggest bank BNP Paribas one of the largest financial institutions known to be affected by an extortion campaign that started in Russia and Ukraine before spreading.
The attack hit BNP’s Real Estate subsidiary, a BNP Paribas spokeswoman told Reuters, after a person familiar with the matter had said that some staff computers were blocked on Tuesday due to the incident.
“The necessary measures have been taken to rapidly contain the attack,” she said.
BNP Paribas Real Estate provides advisory, property and investment management and development services mostly in Europe.
In Austria, a federal police spokesperson reported government-backed Computer Emergency Response Team (CERT) saying “a small number” of international firms appeared to be affected, with tens of thousands of computers taken down.
In the United States, the multinational law firm DLA Piper also reported being hit. Hospitals in Pennsylvania were being forced to cancel operations after the attack hit computers at Heritage Valley Health Systems, a Pennsylvania health care provider, and its hospitals in Beaver and Sewickley, Penn., and satellite locations across the state.
Cadbury factory in Australia had to halt production late on Tuesday after computer systems went down.
Some experts believe ransomware is based on an older variant, originating from the GoldenEye malware in December 2016.