Fresh of this week’s latest global cyber attack, the US government warned that nuclear and energy sectors could be the target of future attacks.
The warning was the latest event to highlight the power industry’s vulnerability to hacking.
Since at least May, hackers used tainted “phishing” emails to “harvest credentials” so they could gain access to networks of their targets, according to a joint report from the US Department of Homeland Security and Federal Bureau of Investigation.
The report provided to the industrial firms was reviewed by Reuters on Friday. While disclosing attacks, and warning that in some cases hackers succeeded in compromising the networks of their targets, it did not identify any specific victims.
“Historically, cyber actors have strategically targeted the energy sector with various goals ranging from cyber espionage to the ability to disrupt energy systems in the event of a hostile conflict,” the report said.
Homeland Security and FBI officials could not be reached for comment on the report, which was dated June 28.
The report was released during a week of heavy hacking activity.
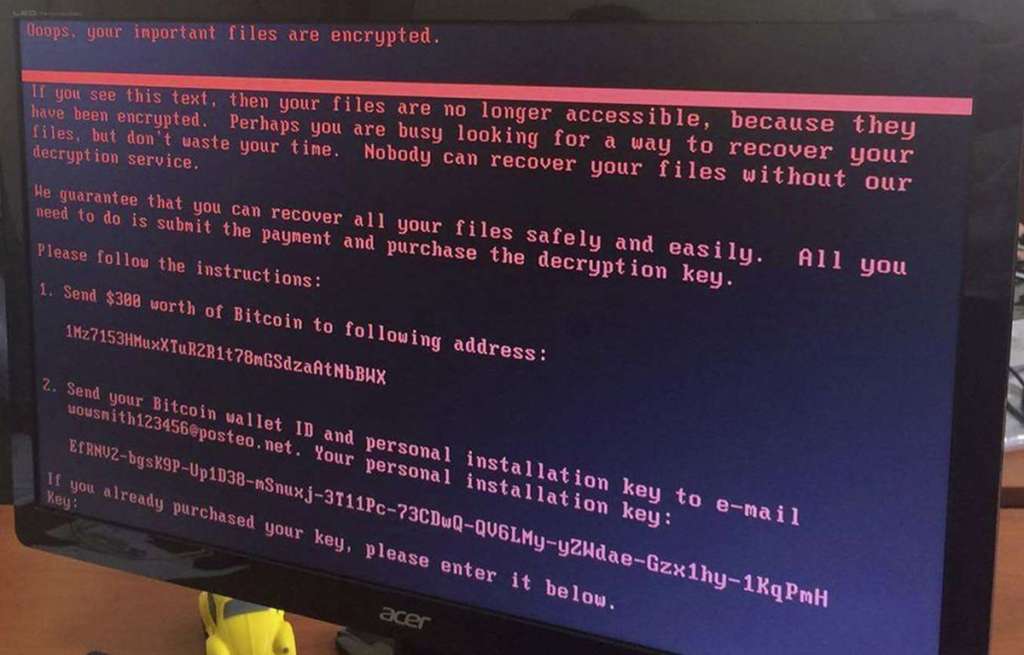
A virus dubbed “NotPetya” attacked on Tuesday, spreading from initial infections in Ukraine to businesses around the globe. It encrypted data on infected machines, rendering them inoperable and disrupting activity at ports, law firms and factories.
On Tuesday the energy-industry news site E&E News reported that US investigators were looking into cyber intrusions this year at multiple nuclear power generators.
Reuters has not confirmed details of the E&E News report, which said there was no evidence safety systems had been compromised at affected plants.
The activity described in the US government report comes at a time when industrial firms are particularly anxious about threat that hackers pose to their operations.
Industrial firms, including power providers and other utilities, have been particularly worried about the potential for destructive cyber attacks since December 2016, when hackers cut electricity in Ukraine.
US nuclear power generators PSEG, SCANA Corp and Entergy Corp said they were not impacted by the recent cyber attacks. SCANA’s V.C. Summer nuclear plant in South Carolina shut down on Thursday due to a problem with a valve in the non-nuclear portion of the plant, a spokesman said.
Another nuclear power generator, Dominion Energy, said it does not comment on cyber security.
Two cyber security firms said on June 12 that they had identified the malicious software used in the Ukraine attack, which they dubbed Industroyer, warning that it could be easily modified to attack utilities in the United States and Europe.
Industroyer is only the second piece of malware uncovered to date that is capable of disrupting industrial processes without the need for hackers to manually intervene.
The first, Stuxnet, was discovered in 2010 and is widely believed by security researchers to have been used by the United States and Israel to attack Iran’s nuclear program.
The US government report said attackers conducted reconnaissance to gain information about the individuals whose computers they sought to infect so that they create “decoy documents” on topics of interest to their targets.
In an analysis, it described 11 files used in the attacks, including malware downloaders and tools that allow the hackers to take remote control of victim’s computers and travel across their networks.
Many businesses still struggled Friday to recover hopelessly scrambled computer networks, collateral damage from a massive cyberattack that targeted Ukraine.
The Heritage Valley Health System could not offer lab and diagnostic imaging services at 14 community and neighborhood offices in western Pennsylvania. DLA Piper, a London-based law firm with offices in 40 countries, said on its website that email systems were down; a receptionist said email hadn’t been restored by the close of business day.
Dave Kennedy, a former Marine cyberwarrior who is now CEO of the security company TrustedSec, said one US company he is helping is rebuilding its entire network of more than 5,000 computers.
The cyberattack that began Tuesday brought even some Fortune 1000 companies to their knees, experts say. Kennedy said a lot more “isn’t being reported by companies who don’t want to say that they are hit.”
The malware spread so quickly, worming its way automatically through interconnected private networks, as to be nearly unstoppable. What saved the world from digital mayhem, experts say, was its limited business-to-business connectivity with Ukrainian enterprises, the intended target.
Microsoft said NotPetya hit companies in at least 64 nations, including Russia, Germany and the United States. Victims include drug giant Merck & Co. and the shipping company FedEx’s TNT subsidiary. Trade in FedEx stock was temporarily halted Wednesday.